Mostly just notes for myself on configuration and troubleshooting when setting up Hyper-V for my homelab. You can find more details about hardware and other stuff like diagrams in the link above.
This post is strictly just configuration of Hyper-V. The reason I think it’s interesting is because running a server OS like Windows Server on a “non-server” hardware usually is a driver nightmare. No spoiler alerts here.
Warning: most of this blog is just me troubleshooting Intel I226 ethernet cards.
Wish me luck.
Configuration
Setting up the Hyper-V host with the Windows Server 2025 November update:
en-us_windows_server_2025_updated_nov_2025_x64_dvd_2cfcca22.iso
I used rufus to create a bootable USB and inserted it into my server. Following the instructions was a breeze, apart from the fact that it didn’t detect any network adapters(my server has three).
| Name | Interface Description |
|---|---|
| Ethernet | Intel(R) Ethernet Network Adapter I226-T1 |
| Ethernet 2 | Intel(R) Ethernet Network Adapter I226-T1 |
| Wi-Fi | Intel(R) Wi-Fi 6 AX200 160MHz |
The main issue here was that at this point I didn’t have the actual description for the drivers and as the certified idiot I am I had already installed Windows Server over the Windows 11 OS that came with the device once I got it. I downloaded the official Intel® Ethernet Controller I226-V drivers, but they wouldn’t install on the system.
Installing Intel I225-V and Intel 226-V on Windows Server 2025
After some research it seems that not only are the I226-V (and I225-V) pretty unreliable, they’re quite a bit annoying overall. I ended up combining advice from both reddit threads and The proper way to install Intel I225-V into Windows Server. into the following guidance:
- Downloaded the official drivers from the link above - I moved it over to the server with a USB-stick.
- Extract the “Wired_driver_30.5_x64.zip” file:
Expand-Archive Wired_driver_30.5_x64.zip
- Navigate to the
PRO2500folder. - Navigate to the
Winx64\WS2022folder. - Open the
e2f.inffile in notepad - notice the current version display in the file.
[Manufacturer]
%Intel% = Intel, NTamd64.10.0...17763, NTamd64.10.0.1..17763
- Find your windows version - (run
winverin pwsh) . - Replace all old windows version references with your system version.
- In my case the system version was 20348.
- I opened the file in notepad and did a find and replace where I changed the current 17763 for my system version.
- Save the file.
- Reboot while holding shift and select the advanced option to disable driver signature enforcement.
- Use
pnputilto add the driver (you can also just right-click the file and install).
pnputil -i -a e2f.inf
- Open
devmgmt.mscand find the network cards and get into the driver installation/update wizard. - Click “I have a disk” or “Browse my computer for drivers”.
- Click “Let me pick from a list of available drivers on my computer” and select the manufacturer called just Intel.
- Scroll to the bottom, here you should find the Intel 225-V and 2226-V drivers.
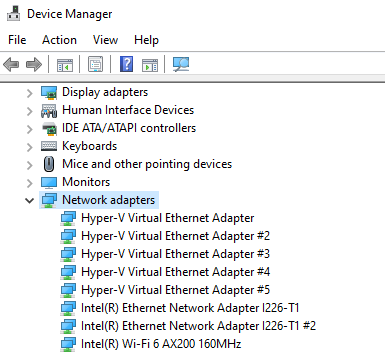
Drivers installed, all adapters showing up as expected:
After all that, I finally get a working connection to my lab router after setting a static IP of 10.13.38.100 and the routers gateway of 10.13.38.1:

I wish this was my last trouble with networking, but later on I try to set up a squid proxy and boy do I troubleshoot for like a decade only to find out I forgot to remove a test route. More on that breaking story later on…
Enabling RDP
For enabling RDP, it’s pretty straight forward in system properties under remote to allow remote connections to this computer, or we can do it via powershell.
# Enable RDP connections
Set-ItemProperty -Path 'HKLM:\System\CurrentControlSet\Control\Terminal Server' -Name "fDenyTSConnections" -Value 0
# Open firewall
Enable-NetFirewallRule -DisplayGroup "Remote Desktop"
# Start the remote desktop service
Start-Service -Name "TermService" -ErrorAction SilentlyContinue
Setting up Hyper-V
- Go into Server Manager
- Install the Hyper-V role
- Profit?
Hyper-V Virtual Switches
For all new virtual switches we get the choice of External (binds a physical adapter so VMs can access a physical network), Internal (only usable by virtual machines on the computer, and between the VMs and the physical computer) or Private (only usable between VMs).
I set up the following networks:
| Name | Type | Description | Physical Adapter Link | IP space |
|---|---|---|---|---|
| Core | Internal | Management network for my Defender for IoT lab | N/A | 192.168.0.0/24 |
| VSwitch-Internal-Lab | Internal | Lab network for my Active Directory lab | N/A | 10.0.0.0/24 |
| VSwitch-SPAN-Azkaban | External | External network for connecting my Defender for IoT sensor to my IoT network | Wi-Fi | 172.16.0.0/24 |
| VSwitch-INET-Cronos | External | Management interface for RDP and proxy server | Ethernet | 10.13.*.0/24 |
I’ll cover a bit more about the VMs and the networking later, but this basically illustrates the way it’s currently set up to work:
flowchart LR
NET1[Core]
NET2["VSwitch-Internal-Lab"]
NET3["VSwitch-SPAN-Azkaban"]
NET4["VSwitch-INET-Cronos"]
MGMT[MGMT Computer]
LABR[Lab router] --> LABR1["Cronos network"]
H{Hyper-V}
H --- DC01[[DC01]]
H --- WS01[[WS01]]
H --- D4IOT[[D4IOT]]
H --- PROXY[[Squid-proxy]]
LABR1 --> |Ethernet| NET4
MGMT --> LABR1
DC01 --> NET2
WS01 --> NET2
NR[Router] --> NR1["Azkaban network"]
NR1 --> IOT[IoT Devices]
NR1 --> NET3
IOT -.-> NET3
NET2 -.-> |Proxy| PROXY
PROXY --> NET4
D4IOT --> |Management network| NET1
D4IOT --> |Sensor network| NET3
NET4 --> |Remote MGMT| H
The idea is that by connecting to my lab router, I can RDP into the Hyper-V host for management. The Cronos network is set up to be the management and outbound proxy network. This will change in the future, I just need a new lab router and/or switch to make use of my second NIC properly.
The internal AD lab has no default outbound access, but the Squid-proxy is connected to the internet via Cronos and the AD lab network relies on Squid to proxy the traffic to the selected endpoints - this is configured to be only the required Defender for Endpoint/Identity URL endpoints at the moment.
My normal home router has recently gotten an IoT-network function (with AP isolation, which I currently have disabled for testing purposes) so I set that up as the Azkaban network and the Hyper-V host connects to that network using a Defender for IoT appliance sensor that has the Wi-Fi card in the server brigded to it.
There are some extra configuration steps to set up the Hyper-V virtual switches with networks, but I will cover that when I cover the configuration of the different servers and labs.
Next steps
The lab runs OK for just me at the moment, but part of the idea is to validate some ideas related to Active Directory and Entra ID hybrid setups possibly with friends. The virtual machine also stands behind the lab router for ease of config at the moment - next iteration of the lab will have the server stand in front of the lab router using OpenSense or something similar.